1. Storage and server technology

Servers are an indispensable component in information technology systems, considered the central brain of the entire system, and are divided into many different types depending on usage needs. We offer product lines from many manufacturers such as Cisco UCS, HP, IBM, Dell… These are divided into three main segments:
-
Entrance Level Servers: Designed for low-demand needs, mainly for small businesses or applications that do not require high configurations.

-
Midrange Level Servers: Designed for small and medium-sized businesses, capable of supporting systems requiring high processing speeds and virtualization.

-
Enterprise-class servers: Designed for systems with very high performance and virtualization requirements, supporting multiple processors, large amounts of memory, and providing very high I/O and data transfer bandwidth. This segment is represented by servers with a Blade architecture.

2. Virtualization Solutions

Virtual Desktop Infrastructure (VDI) is a solution that uses computing resources from servers combined with virtualization technology to create a system of workstations, which are then virtual machines. Users access the system and are allocated virtual machines for remote use.
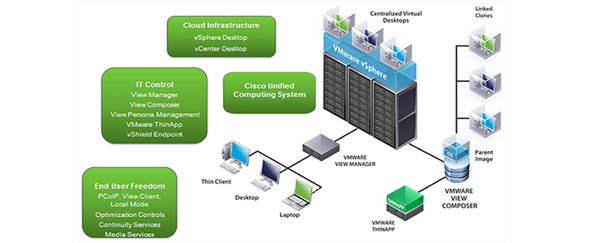
Images of the interfaces of the running virtual machines are transmitted to the user's terminal screen, and user operations (keyboard, mouse, etc.) proceed completely normally through remote display protocols (Desktop Display Protocol) established between the user's access device and the workstation within the data center.
3. Collaboration Solution

Currently, there are many models for deploying Unified Communications systems; however, any Unified Communications system must rely on a central call processing device, the Cisco Unified Communications Manager.
The Cisco Unified Call Manager is the call processing component in Cisco's Unified Communications system. It extends enterprise voice capabilities and transforms them into call-packaging devices such as IP Phones, multimedia processing devices, VoIP gateways, and multimedia applications. Furthermore, it integrates services such as messaging, multimedia conferencing, contact centers, and interactive multimedia responses with IP telephony solutions through Cisco Unified Call Manager application programming interfaces (APIs).
3.1 Basic Components of an IP-based Voice System
Central PBX:
+ The Cisco Unified Communication Manager (formerly known as Cisco CallManager or IP PBX) is the central hub for handling all voice calls for the IP Telephony network. Cisco Unified Communication Manager enhances the capabilities of the IP voice network through network devices such as IP phones, media processing devices, VoIP gateways, and multimedia applications.
.jpg)
Voice Gateway System:
+ A voice gateway provides the ability to communicate between different types of voice control signaling protocols. For example, a voice gateway provides the ability to communicate between voice systems using the H.323 protocol and PBX systems using other protocols through a protocol converter system. It provides the ability to connect IP telephony systems with PSTN systems, traditional PBX systems, or connect to analog phones or fax machines.
Gatekeeper System:
+ The Gatekeeper network element is responsible for managing the registration, acceptance, and status of terminal devices and gateways. It determines the path for transmitting call signaling and content for each call, and can also participate in zone management, call processing, and call signaling.
Endpoint System:
+ Endpoint communication devices include desk phones, voice software installed on PCs, and each of these devices has Ethernet connections
3.2 VoIP Deployment Models
The IP Telephony system deployment model is based on the following platform:

+ Single-Site Model: The Cisco Unified Communication single-site deployment model includes a single call center located at a single site. IP Telephony services are not provided over a WAN. In this deployment model, all equipment serving the IP Telephony system, including the PBX, voice gateway, and endpoint, is located at a central site, and voice data is centralized at a single point.
+ Multi-Site Model with Centralized Call Center: The Multi-Site deployment model is designed with a call center located at the headquarters, providing VoIP services to remote sites connected via the IP WAN infrastructure. The WAN handles the transport of VoIP traffic between the central site and remote sites. Remote sites rely on the Cisco Unified Communication Manager system, deployed as a cluster, to use services such as Voice Mail and IVR (interactive voice response).
+ Distributed Call Handling Multipoint Communication Model: This model is only applied when a Cisco Unified Communication Manager Cluster is not large and powerful enough to support the entire system, either due to geographical or organizational constraints.
4. Data Center Infrastructure Support Solutions

4.1 Power Supply System Design
The data center uses the building's grid power, with an automatic transfer switch (ATS) system between the grid and the building's generator. The data center's main switchboard will power the uninterruptible power supply (UPS) system, which will provide stable power to the IT equipment.
The data center's main switchboard will also power the UPS, the CRAC switchboard will power two Uniflair cooling units, and the ELV switchboard will power household appliances and lighting.
4.2 Precision Air Conditioning System Design
The data center will be equipped with a precision air conditioning (AC) system to control ambient temperature between 20-24°C and relative humidity between 40-55%. The AC system used in the server room design is a downflow system. The cooling systems are located in the same room as the server racks. The total design capacity meets the electrical power (heat dissipation power) of the IT equipment with N+1 redundancy:
Using 2 cooling systems, providing a cooling capacity of 39kW/machine with 39W of redundancy. To ensure operational efficiency, this design meets N+1 redundancy.
4.3 Security and Fire Protection System Design
Data center entrances are equipped with magnetic card readers and keypads to ensure a high level of access control. The fire protection system uses FM200. The security and fire protection systems are equipped with separate battery power sources, capable of continuous operation for 24 hours in case of power failure.
4.4 Construction Design
All electrical cabling will be routed under the raised floor, and a raised floor will be installed in the data center area. The front facade will be rebuilt with 1-hour fire-resistant drywall including insulation. The drywall will extend from the concrete floor to the false ceiling to ensure absolute airtightness. Entrance doors are 1-hour fire-resistant steel doors.
4.5 Centralized Management System Design
The centralized management system fulfills four main functions:
+ Centralized monitoring of security cameras installed in the data center.
+ Monitoring temperature and humidity in necessary areas within the data center rooms and water leaks.
+ Centralized monitoring and management of UPS, CRAC, and PDU systems distributing power to rack cabinets.
+ Managing and sending alerts based on configured conditions to data center administrators via various methods (SMS, email, etc.).
5. Security Solutions
The air-cooled cooling technology includes one outdoor condenser for each system. The condensers will be located in the rear area of the building.

5.1 RSA SecurID Two-Factor Authentication Solution
With traditional authentication solutions proving insecure, better solutions are needed in today's business environment. A good authentication solution is one that meets the following key requirements:
+ Low cost.
+ Easy and convenient to use and compatible with multiple systems.
+ High scalability and compatibility with other systems.
+ RSA's SecurID two-factor authentication solution operates on the principle that to log into the system, the user must possess two elements: something they know and something they possess. This is similar to withdrawing money from an ATM: you need your ATM card (which you possess) and your PIN (which only you know). Without either the ATM card or PIN, you cannot withdraw money.
-
The RSA SecurID® solution consists of three components:
+ RSA SecurID® Authenticators: These are devices attached to the user. They can be hardware or software and are called Tokens. Customers can choose the device that best suits their needs.
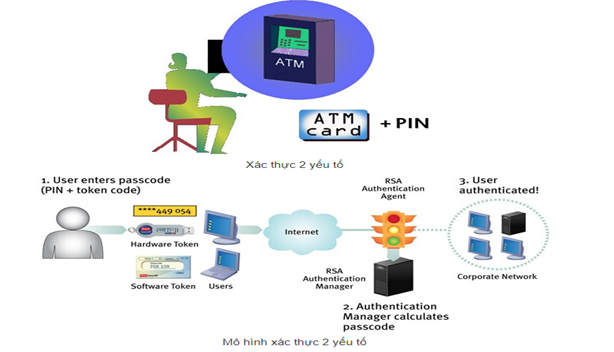
-
If it's a hardware device, the RSA solution allows users to use it anytime, anywhere, on any computer without needing to install any additional software (zero footprint solution).
-
If it's software, it can be installed on laptops, integrated with browsers, or other handheld devices such as PDAs, Wireless Phones, etc. These devices generate different numbers over a certain period of time.
+ RSA Authentication Agent: This is software installed on network access points (e.g., gateways, VPNs, Remote Access Servers, etc.), servers, and other information resources that need to be protected within a business. It acts like a gatekeeper. When a user's login request is received, it receives and forwards the login information to the server with the RSA Authentication Manager component for authentication.

+ RSA Authentication Manager: This is the administrative component of the RSA SecurID solution, used to verify authentication requests and centrally manage authentication policies across the entire enterprise network. RSA Authentication Manager can be scaled to meet any enterprise need. It can authenticate millions of users, including local network users, remote users, VPN users, etc. RSA Authentication Manager is fully compatible with network devices, RAS, VPN, Access Points, etc., from all major manufacturers worldwide. Therefore, with RSA's SecurID solution, users don't have to worry about compatibility issues.
+ RSA Authentication Manager also offers tight integration with standard service systems such as RADIUS, LDAP, etc.
+ Another outstanding feature of RSA that no other provider has is the ability to create multiple independent work areas (realms) and the ability to allow up to 15 RSA Authentication Manager servers to operate on one system.
5.2 IronPort Email Security Solution
-
IronPort has been a leading provider of anti-spam, anti-virus, and anti-spamware devices for organizations ranging from small to Global 2000. IronPort's email security, web security, and management product lines utilize SenderBase (the world's largest threat intelligence data provider) to analyze email and web behavior globally, enabling IronPort devices to effectively and quickly mitigate risks that could negatively impact organizational operations.
-
Solution Model: Customers can use IronPort as a mail gateway for both incoming and outgoing email data.
-
Key Features of IronPort: IronPort allows for detailed rule settings for individual users or groups of users. For example, if you need to monitor an individual user or a department within a company, IronPort supports LDAP and AD for accessing user or group information. Iron Port Senderbase Network: Iron Port's SenderBase is the world's largest email traffic monitoring network. Collecting approximately 30% of the world's internet data, IronPort's SenderBase network provides real-time observation of threats from around the globe.